Complete Parental Guide for Online Child Exploitation
Complete Parental Guide for Online Child
ALL TOPICS
- YouTube Parental Control
-
- How to see your YouTube history?
- Put parental controls on YouTube
- Delete TikTok Account without Phone Number
- Ways to block YouTube channels
- Ways to Get Somone's IP Address and Hide IP Address
- A complete guide on YouTube parental control
- Kids safe YouTube alternative
- Top 5 TikTok Alternatives
- Methods to restrict YouTube adult content
- Social Media App Parental Controls
- Parental Control Tips
Dec 12, 2025 Filed to: Parenting Tips Proven solutions
What is Online Child Exploitation?
The evolution of the internet has transformed the face of online exploitation. While the internet is known as a good force, there are dark elements within the cyber world who may exploit the internet to further their evil desires. These people primarily rely on the internet to engage, hook up, and ultimately exploit minors who may be online. This advancement has increased how different people, even children are exploited through grooming, sexual abuse, cyberbullying and sex trafficking. Significant developments in the scene have granted different forms of online child abuse. In most cases, online child exploitation takes the form of sexual abuse and cyberbullying. Exposing minors to mature content, coercing and blackmailing children into sexual activity. In some instances, online child exploitation may transform into offline exploitation where the underage children may get abused physically, emotionally or even sexually.
The changing aspect of the internet led to Facebook Founder Mark Zuckerberg calling out for new internet regulations. Zuckerberg felt that law enforcement is facing challenges in keeping up with the negative implications of the internet. Hence the need for a fresh regulatory framework.

What Causes Online Child Exploitation?
Several things could expose a kid to online exploitation. While internet child exploitation manifests itself in the form of either emotional or physical abuse; it is worth taking a look at the breeding ground for these forms of exploitation.
- Apparent absence of supervision
- Neglecting parental controls
- Depression
- Excessive usage of the internet
Online child exploitation as a global concern requires effort from governments, private entities and parents alike. However, most importantly, parents ought to monitor their children's online presence and identify signs of internet exploitation.
What are the Signs of Online Child Exploitation?
Your child could manifest several symptoms as proof of online child exploitation. These signs could help you take necessary steps against further exploitation and save your kid from emotional trauma.
Defiant behavior - rebellious behavior is one red flag for emotionally abused minors. Mostly persistent unusual fears, depression and unusual anxiety could easily create a defiant attitude.
Runaway attempts - Online blackmailers may coerce children into running away from their homes. There have been cases of internet criminals daring threats on minors if they failed to meet them. Hence, most of the kids will make several attempts to run away from their homes to meet their contact.
Behavioral changes - hyperactivity, aggression, hostility or anger are potential behavioral changes you are likely to encounter in an exploited child.
How Online Child Explorers Find Victims?
The majority of online predators use social media platforms to lure kids. Pew Research Centre found out that at least 95% of children owned a phone in 2018. On average, the study established that teens spend at least nine hours of screen time every day.
One in five 13-19 aged teens have reported to have posted a semi or completely nude image of themselves. The study also suggested that most of the girls send these pictures to males friends they consider as boyfriends. The boyfriends in return demand more pictures threatening to share the ones they have. In fact, most of the teens that turn to social media are looking for attention and acceptance. Hence they become easy prey for sexual predators.
Usually, they will groom them for sexual activity by manipulating their vulnerabilities. Grooming is where a criminal will build trust around a child in a bid to secure time alone with the children. There are three phases of grooming, scouting, manipulation and trapping. Scouting involves identifying a vulnerability in a kid, then manipulating the kid with either expensive gifts or promises and finally they trap them for servitude, sex trafficking or prostitution.
Methods
- Talk to the kids about online safety and listen to them. Sometimes children could remain silent even after undergoing sextortion through the internet. This is because they are afraid of more trouble for breaking the rules.
- Spend more time with the kids while they use the applications or play games - help children identify risks on new platforms and encourage them to raise concern over suspicious adults.
- Set rules for how a child should use the internet, set times restrictions and supervise the online accounts.
A third-party application such as FamiSafe could help parents control their children's internet usage.
Introducing FamiSafe
FamiSafe provides an important tool for parental control. The application helps parents track their kid's online engagements and keeps safety at heart. Parents require assistance in parenting and therefore the need for a third party utility is ideal. The application equips parents and guardians with an interactive interface that includes several parental control features. These features include Web filtering, application usage and block, activity reports, location history and geo monitoring. Main Features of FamiSafe
Below are the main features of FamiSafe that position it as an important tool for parenting.
- Track – location history and real-time location.
- Limit – Application usage is limited and also screen time is restricted.
- Monitor – Provides a log of browser history and a report on all activities.
- Detection – Detects content that is deemed to be suspicious and also tracks.
- Block – Provides the ability to block content
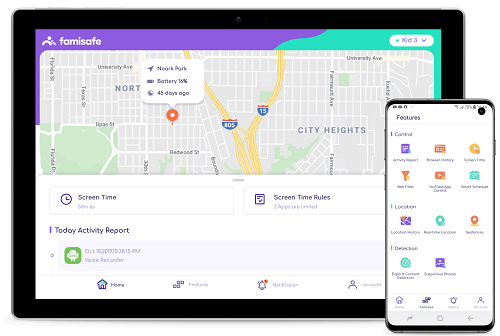
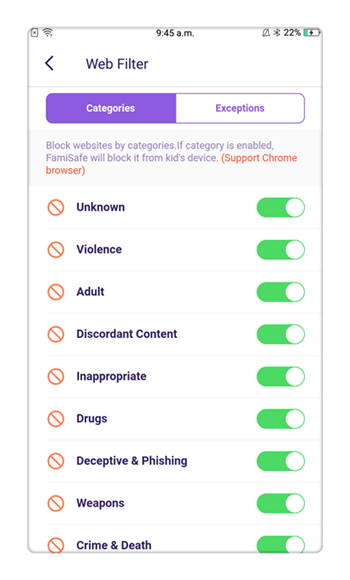
- Web Filtering
- Location Tracking & Geo-fencing
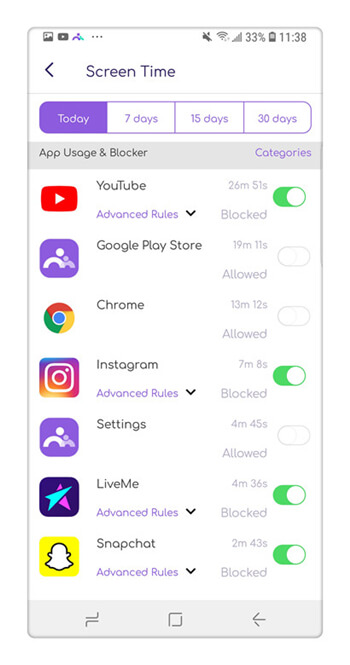
- App Blocker & App Activity Report
- Screen Time Limit & Schedule
- Explicit Content & Suspicious Photos Detection
Screen Time and Smart Schedule
If you enable this feature, the kids will not be distracted and can easily focus on the task at hand. Kids will not be distracted easily if you enable this feature for they will easily focus on the task at hand. The feature can be enabled on a particular platform for kids to focus on their specific duty. This feature can enable kids to balance their different schedules, including work, school and internet time.
Browser History and Web Filtering
This feature detects filtration of potential harmful internet usage and also allows remote tracking of web history, making kids stay away from online violence, porn, gambling and other sites which are risky. This calls for parents to double-check their children's history while offline or if deleted.
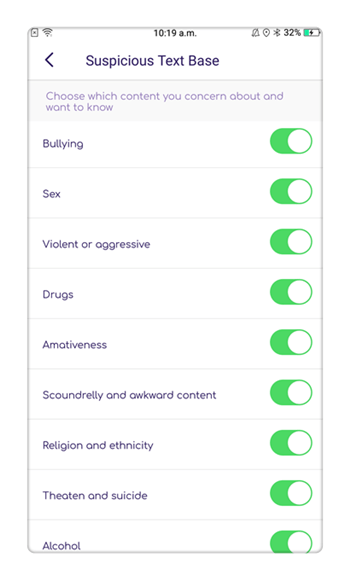
Suspicious Explicit Content Detection
FamiSafe comes in handy with parental control keywords that are flexible and can provide and track down real down warnings of adult content, sex extortion, cyberbullying and depression. To prevent pedophiles, sex and internet blackmailers from getting whatever they want and in case of suspicious content, parents usually receive real-time signals. This feature helps detect explicit and dangerous content on various mobile applications such as YouTube, Twitter, Kik, Facebook and WhatsApp.

Parents App Block and Usage
Armed with information, parents can identify and block malicious applications. They can also double-check the daily activities that are provided by FamiSafe because it will enable them to track down their kids' daily application usage and most used applications. This will additionally, allow them to track down digital trends among the young generation.
Conclusion
Are you a parent that lacks the resources and time to keep track of your children's internet usage? Third-party applications such as FamiSafe provides you with handy tools for tracking your children's online activity. The idea is to help you track potentially risky activity that could make your kid fall victim of online child exploitation.


Thomas Jones
chief Editor