Top 10 Most Reliable Cyber Security Tools or Softwares
Top 10 Most Reliable Cyber Security Tool
ALL TOPICS
- YouTube Parental Control
-
- How to see your YouTube history?
- Put parental controls on YouTube
- Delete TikTok Account without Phone Number
- Ways to block YouTube channels
- Ways to Get Somone's IP Address and Hide IP Address
- A complete guide on YouTube parental control
- Kids safe YouTube alternative
- Top 5 TikTok Alternatives
- Methods to restrict YouTube adult content
- Social Media App Parental Controls
- Parental Control Tips
Apr 30, 2026 Filed to: Parenting Tips Proven solutions
Technology has surpassed and improved the traditional methods of communication, payments, and sharing of information. Every small, medium, and large-scale business is at the risk of cyber-attack due to the involvement of technology and expert cyber crooks. They dare to gain access even to the firmly secured sites with end to any encryption and are highly adept at breaking the security of any technology. Cybersecurity tools encompass technologies, and its practice helps prevent attacks, damage, or unauthorized access to any device, network, or programs. In the article below, we curate a list of some cybersecurity software that you must know.
10 cybersecurity tools or software
Some of the best cybersecurity tools or software are here as shown:
1. WebTitan
Cyber attacker applies various strategies to hack and steal data from your device. WebTitan is a web filtering, a DNS based cybersecurity tool through which you can prevent phishing and malware attacks. It allows you to block pornographic, violent speeches, and unimportant online materials.
Find out more at https://www.webtitan.com/.
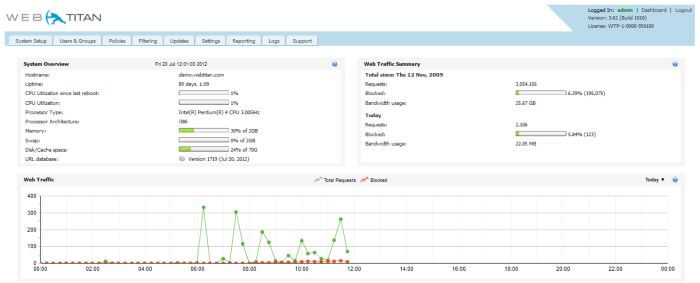
Features:
- Filters websites into a total of 53 categories social media, news, etc.
- Make your internet usage policy for your company
- Most features are API driven
- Removes useless contents from being shown on the systems
- The cloud-based solution so consume less space and works faster
- Provides an extensive report on the browsing activity of employees
Pros:
- Simple to set up in 3 steps
- Allow to control multiple locations using one portal only
- No clients or software required
Cons
- Cost $0.90 per user every month
- For a beginner, it may seem complicated
2. Acutenix
Acutenix is a compact cybersecurity tool to deal with web attacks and stop malicious software from affecting the systems in your organization. It is mainly a web scanning tool and finding vulnerabilities better than traditional black-box testing scanners.
Visit https://www.acunetix.com/ to know more about Acutenix.

Features
- Performing auditing and scanning of web applications
- Suitable for government, military, education and in many other areas
- Serves you the power to integrate with any software development tools
- Reduce cyber attack at a low cost
Pros
- Vulnerabilities get collectively shown in one page
- Quite easy to review scan results
- Responsive web interface
Cons
- Not available for iOS and Android mobile devices
- Lacks few features like incident management, endpoint management, and others
3. FamiSafe
The most stunning parental control cybersecurity software is here. FamiSafe is an integrated app for your kids who get exposed to obscene content on the net. Some sites are dangerous to visit, especially those that have adult content on their pages. These types of sites are the easiest way for hackers to attack the user’s device. Decide it yourself and monitor what kids should see and what they should not.
https://famisafe.wondershare.com/
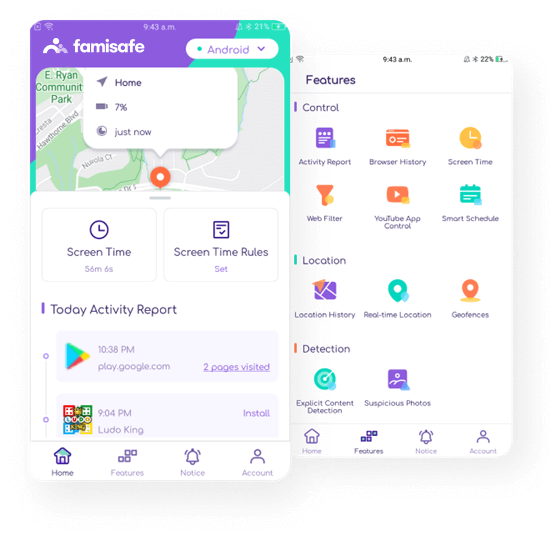
Features
- Ability to filter web contents and produce only those search results that are suitable for you and your kids
- It checks and notifies about a suspicious photo when kids receive
- Helps in monitoring screen time usage
- Provides real-time location and history of wherever kids went
- Also helps in blocking websites and installed applications
Pros:
- Set a time limit for the screen usage
- Let’s you block addictive applications
- Works without jailbreaking
Cons:
- Comes with restrictions in iPhone
- You won’t get the exact location when the location service is off
4. Mimecast
Mimecast is a perfect cybersecurity software for email management in your organization. Founded in 2003, today, Mimecast has over 34,000 customers worldwide.
https://www.mimecast.com/
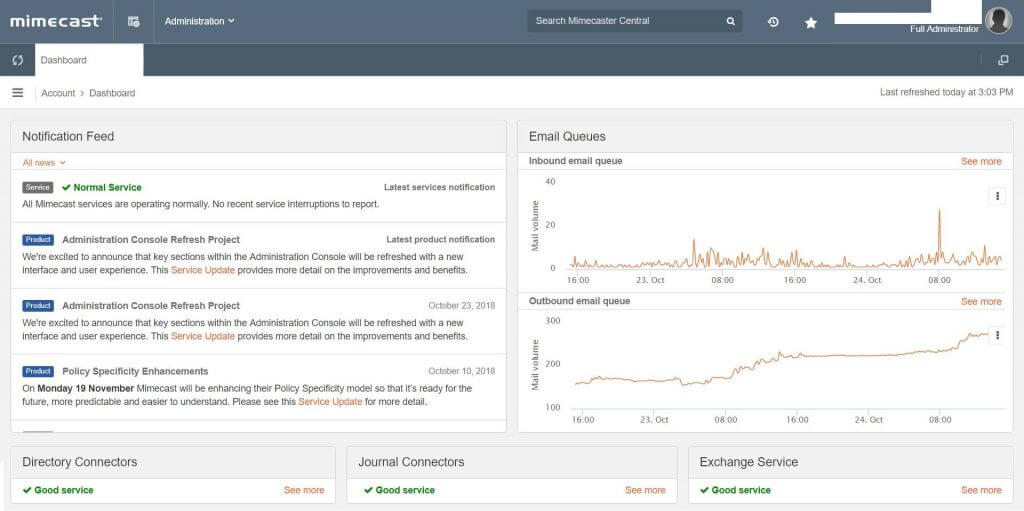
Features:
- Protects from every kind of cyber attack
- Filters spam and suspicious emails and inspect attached files for virus
- Provides encryption to the outgoing emails for safe delivery
- Uses multi-layered protection from malware and threatening
- Prevents the leakage of data
Pros:
- Powered with the intuitive management console
- Supports a robust and quick search feature
- Runs in the background without impacting the daily tasks
Cons:
- Some email will be on hold without any prior notification leading to late delivery of emails
- Links attached in emails are allowed to open after scanning and asking the user if it is safe to open it or not
5. Snort
It is an easy to use network intrusion detection system and intrusion prevention system for Linux, Windows, and Mac users. It checks the system for a malicious activity performed and violation of policy.
https://www.snort.org/
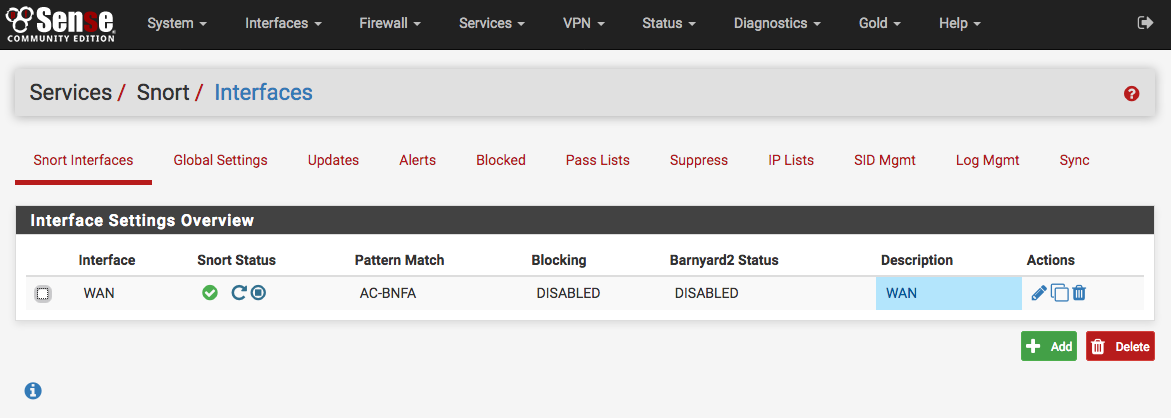
Features:
- Made for the business of information technology and high educational sector
- Gives real-time analysis of traffic
- Fast in identify potential threats and taking action against them
- Able to process a 400Mbit/node.
Pros:
- Open source cybersecurity software
- Scalable meaning it can be employed on any network environment
Cons:
- Impossible for beginners to set up
- Takes too much time on windows to install
- Learning to use it will take time
6. Webroot
Businesses, as well as individuals, can use Webroot. It is a lightweight cloud-based antivirus solution. Choose Webroot for intelligent protection to your system and devices.
https://www.webroot.com/in/en
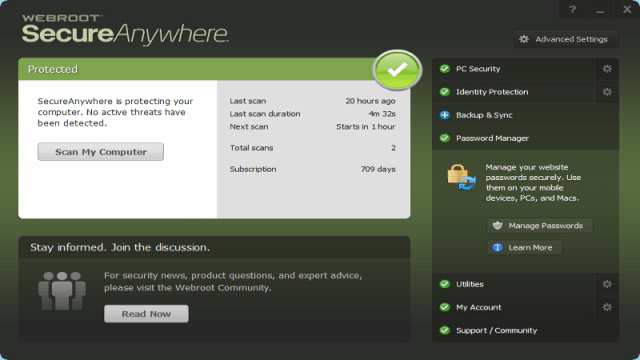
Features:
- No need to have any experience beforehand to use this cybersecurity software built for the next generation
- Works without any lag
- Available on multiple platforms
Pros:
- Thin and competitive
- The deployment process is simple to implement
Cons:
- Sometimes, it fails to detect all types of virus
- Bugs are a concern
- Not appropriate for military uses
7. Dashlane
It is the most awaiting password management cybersecurity software. Dashlane keeps your passwords secured for a long time and lets you access it whenever you need it.
https://www.dashlane.com/
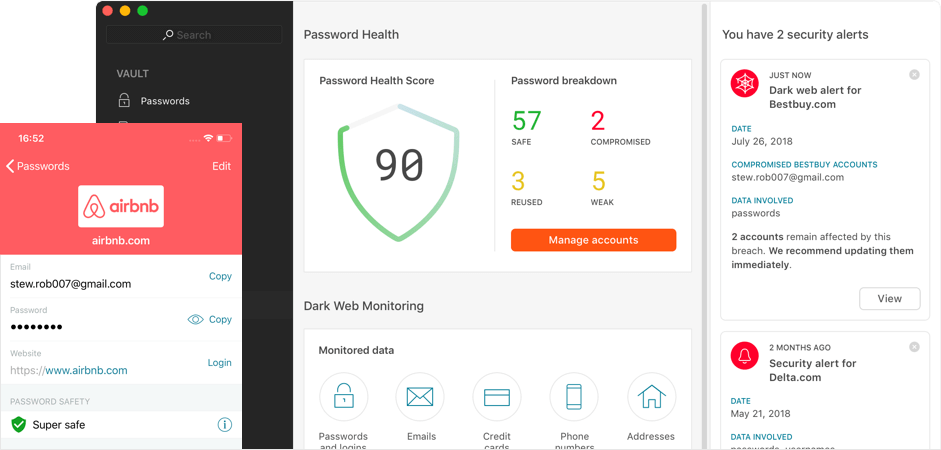
Features:
- It can store many passwords
- Can autosave passwords and enter them automatically while logging in
- Protect passwords with full proof security
- Uses AES-256 password and data encryption
Pros:
- Dashlane patented its security architecture with USPTO
- Helps in creating a strong password for you when you can’t
Cons:
- All the features only work on the Dashlane browser in Android devices.
- Similar software is already available online with better functionality.
8. Teramind
It is a leader in cybersecurity software for monitoring employees, finding unreasonable risks, and preventing loss of data. It will help in boosting the productivity of employees at your organization. It even works for organizations with a large number of employees.
https://www.teramind.co/
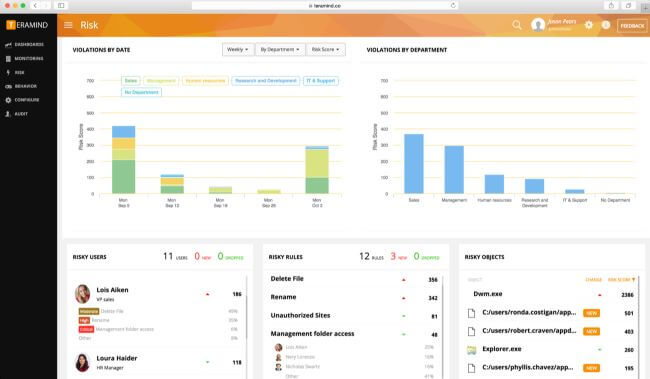
Features:
- Fully automated software
- Packed with OCR on-screen recording feature
- Supply options to change from stealth to revealed mode
- It also records keystrokes
Pros:
- Built-in admin dashboard
- Smooth working user experience
Cons:
- Remove control feature doesn’t work properly
- Little complicated in understanding monitoring feature
9. Barkly
Individuals or organizations using antivirus protections software must try Barkly for endpoint protection. The chances of false positives are very less. It is a perfect blend of robust security, smart technology, and simple management.
https://www.cyberdb.co/vendor/barkly/
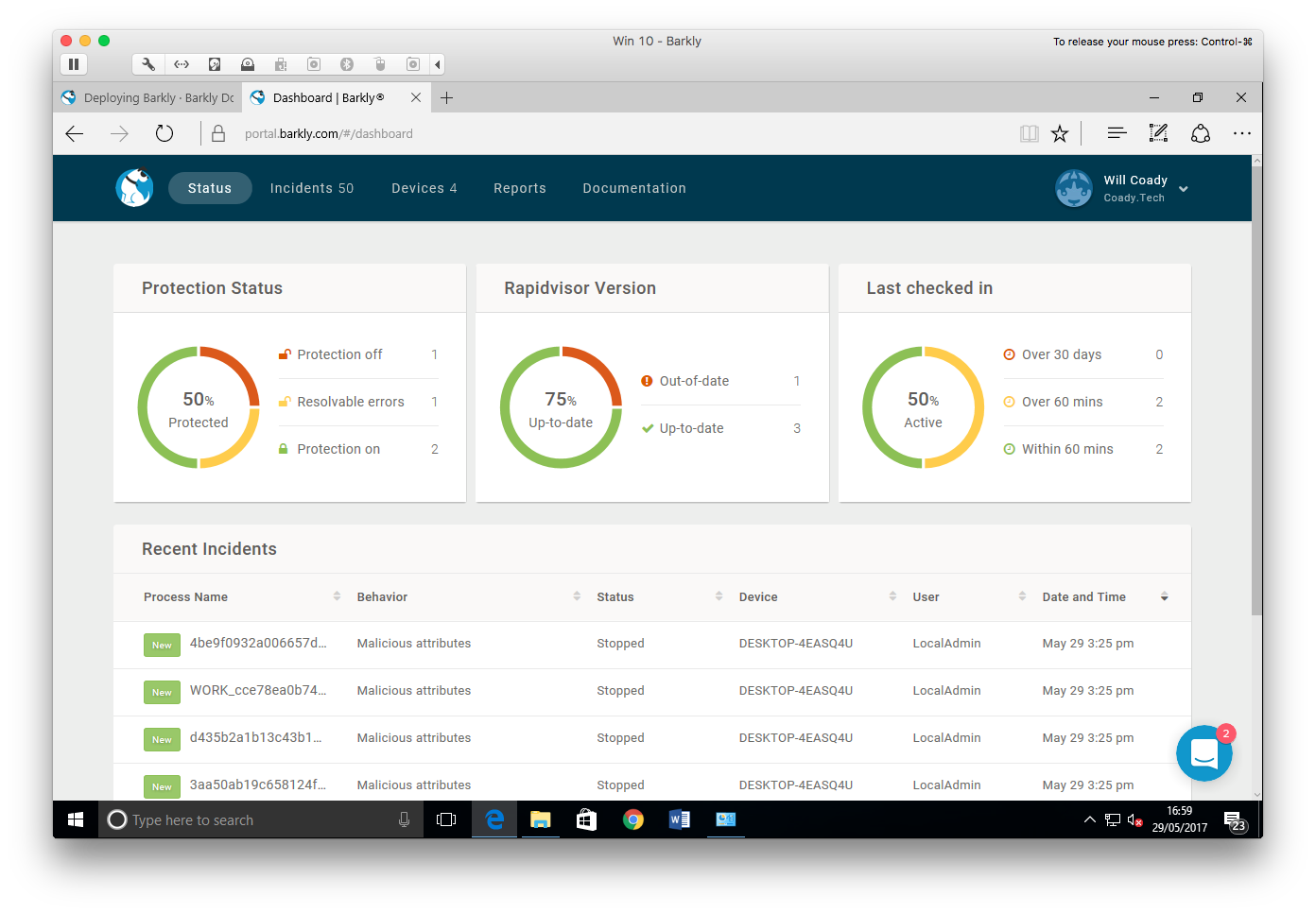
Features:
- Considered as the best cybersecurity software
- Blocks cyber threats in all the vectors
- Comes with 3 level architecture pattern
- Featured with blacklisting, whitelisting, incident and endpoint management, AI/machine learning, behavioral analytics and many more
Pros:
- Requires low resource to work and run smoothly
- Great tool for everyone for avoiding security risks
Cons:
- Lacks many features
- Limited data in the documentation
10. Siteblock
Siteblock, based on cloud service, is the last cybersecurity software we are going to talk about today. Launched in 2008 to protect every website on the Internet, Siteblock today is protecting around 12 million sites from attacks and threats.
www.sitelock.com

Features:
- It keeps your site and its code, web applications completely safe
- Increase the number of visitors on your site
- Check malware daily for keeping the consistent traffic
- Detect all the installed apps on your website for vulnerability
Pros:
- Everything is simplified and straightforward to use
- Recognizes threats with the help of 306-degree monitoring
- 24/7 live support team is always there for you to help
Cons:
- It is not developed for Mac, Windows or iOS
What can FamiSafe do for cybersecurity on kids?
a. Web filtering in FamiSafe is a superb feature for blocking adult sites. It also promotes the safe search on the internet by blocking websites of the category of your choice. You choose what your kids can search, view, and watch.
b. When anyone tries to send an abusive or misleading text message to your kid, FamiSafe will automatically identify and hide them. It creates a safe environment for your kid.
c. Cyberpunks can try to gain access to a kid’s phone, and it is much easier than hacking adult phones. Sending suspicious photos and inappropriate content is a way for them to steal information. They will even infect the device with the virus.
- Web Filtering
- Location Tracking & Geo-fencing
- App Blocker & App Activity Report
- Screen Time Limit & Schedule
- Explicit Content & Suspicious Photos Detection
Modern hackers are adept at playing with network security and cracking passwords to manipulate devices and networks. Cybersecurity tools act as a shield for protecting devices, websites, and systems and beating hackers.


Joanne Croft
staff Editor